New 2020 CCIE/CCNP 350-401 ENCOR exam questions from PassLeader 350-401 dumps! Welcome to download the newest PassLeader 350-401 VCE and PDF dumps: https://www.passleader.com/350-401.html (391 Q&As –> 408 Q&As –> 436 Q&As –> 475 Q&As –> 549 Q&As –> 612 Q&As –> 735 Q&As –> 770 Q&As –> 793 Q&As –> 822 Q&As –> 992 Q&As –> 1025 Q&As –> 1129 Q&As –> 1198 Q&As –> 1239 Q&As) [Lab Simulations Available]
P.S. Free 2020 CCIE/CCNP 350-401 ENCOR dumps are available on Google Drive shared by PassLeader: https://drive.google.com/open?id=1nv6C6Az-yuR5kOXg8FV3gytDer_usQBX
NEW QUESTION 375
A company has an existing Cisco 5520 HA cluster using SSO. An engineer deploys a new single Cisco Catalyst 9800 WLC to test new features. The engineer successfully configures a mobility tunnel between the 5520 cluster and 9800 WLC. Clients connected to the corporate WLAN roam seamlessly between access points on the 5520 and 9800 WLC. After a failure on the primary 5520 WLC, all WLAN services remain functional; however clients cannot roam between the 5520 and 9800 controllers without dropping their connection. Which feature must be configured to remedy the issue?
A. mobility MAC on the 5520 cluster
B. mobility MAC on the 9800 WLC
C. new mobility on the 5520 cluster
D. new mobility on the 9800 WLC
Answer: B
NEW QUESTION 376
In a Cisco SD-Access solution, what is the role of the Identity Services Engine?
A. It is leveraged for dynamic endpoint to group mapping and policy definition.
B. It provides GUI management and abstraction via apps that share context.
C. it is used to analyze endpoint to app flows and monitor fabric status.
D. It manages the LISP EID database.
Answer: C
NEW QUESTION 377
What is the data policy in a Cisco SD-WAN deployment?
A. list of ordered statements that define node configurations and authentication used within the SD-WAN overlay
B. set of statements that defines how data is forwarded based on IP packet information and specific VPNs
C. detailed database mapping several kinds of addresses with their corresponding location
D. group of services tested to guarantee devices and links liveliness within the SD-WAN overlay
Answer: B
NEW QUESTION 378
In a three-tier hierarchical campus network design, which action is a design best-practice for the core layer?
A. provide QoS prioritization services such as marking, queueing, and cl ssification for critical network traffic
B. provide redundant Layer 3 point-to-point links between the core devices for more predictable and faster convergence
C. provide advanced network security features such as 802. IX, DHCP snooping, VACLs, and port security
D. provide redundant aggregation for access layer devices and first-hop redundancy protocols such as VRRP
Answer: A
NEW QUESTION 379
What ate two characteristics of Cisco SD-Access elements? (Choose two.)
A. The border node is required for communication between fabric and nonfabric devices.
B. Fabric endpoints are connected directly to the border node.
C. Traffic within the fabric always goes through the control plane node.
D. The control plane node has the full RLOC-to-EID mapping database.
E. The border node has the full RLOC-to-EID mapping database.
Answer: AD
NEW QUESTION 380
What is YANG used for?
A. scraping data via CLI
B. processing SNMP read-only polls
C. describing data models
D. providing a transport for network configuration data between client and server
Answer: C
NEW QUESTION 381
A customer has completed the installation of a Wi-Fi 6 greenfield deployment at their new campus. They want to leverage Wi-Fi 6 enhanced speeds on the trusted employee WLAN. To configure the employee WLAN, which two Layer 2 security policies should be used? (Choose two.)
A. 802.1X
B. WPA (AES)
C. WPA2 (AES) jWEP
D. OPEN
Answer: AC
NEW QUESTION 382
Which encryption hashing algorithm does NTP use for authentication?
A. SSL
B. MD5
C. AES128
D. AES256
Answer: B
NEW QUESTION 383
Which two actions, when applied in the LAN network segment, will facilitate Layer 3 CAPWAP discovery for lightweight AP? (Choose two.)
A. Utilize DHCP option 17.
B. Configure WLC IP address on LAN switch.
C. Utilize DHCP option 43.
D. Configure an ip helper-address on the router interface.
E. Enable port security on the switch port.
Answer: CD
NEW QUESTION 384
Which two network problems indicate a need to implement QoS in a campus network? (Choose two.)
A. port flapping
B. excess jitter
C. misrouted network packets
D. duplicate IP addresses
E. bandwidth-related packet loss
Answer: BD
NEW QUESTION 385
How does Protocol Independent Multicast function?
A. In sparse mode it establishes neighbor adjacencies and sends hello messages at 5-second intervals.
B. It uses the multicast routing table to perform the multicast forwarding function.
C. It uses unicast routing information to perform the multicast forwarding function.
D. It uses broadcast routing information to perform the multicast forwarding function.
Answer: C
NEW QUESTION 386
Which technology does VXLAN use to provide segmentation for Layer 2 and Layer 3 traffic?
A. bridge domain
B. VLAN
C. VRF
D. VNI
Answer: D
NEW QUESTION 387
What are two methods of ensuring that the multicast RPF check passes without changing the unicast routing table? (Choose two.)
A. implementing static mroutes
B. disabling BGP routing protocol
C. implementing MBGP
D. disabling the interface of the router back to the multicast source
E. implementing OSPF routing protocol
Answer: AC
Explanation:
https://www.cisco.com/c/en/us/support/docs/ip/ip-multicast/16450-mcastguide0.html
NEW QUESTION 388
Under which network conditions is an outbound QoS policy that is applied on a router WAN interface most beneficial?
A. under all network conditions
B. under network convergence conditions
C. under traffic classification and marking conditions
D. under interface saturation conditions
Answer: C
NEW QUESTION 389
What is provided by the Stealthwatch component of the Cisco Cyber Threat Defense solution?
A. real-time threat management to stop DDoS attacks to the core and access networks
B. real-time awareness of users, devices and traffic on the network
C. malware control
D. dynamic threat control for web traffic
Answer: A
NEW QUESTION 390
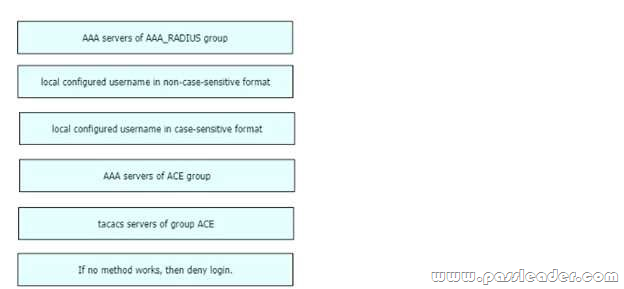
Drag and Drop
An engineer creates the configuration below:
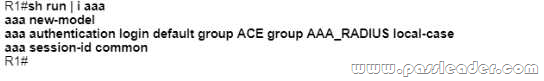
Drag and drop the authentication methods from the left into the order of priority on the right. Not all options are used.
NEW QUESTION 391
……
New 2020 CCIE/CCNP 350-401 ENCOR exam questions from PassLeader 350-401 dumps! Welcome to download the newest PassLeader 350-401 VCE and PDF dumps: https://www.passleader.com/350-401.html (391 Q&As –> 408 Q&As –> 436 Q&As –> 475 Q&As –> 549 Q&As –> 612 Q&As –> 735 Q&As –> 770 Q&As –> 793 Q&As –> 822 Q&As –> 992 Q&As –> 1025 Q&As –> 1129 Q&As –> 1198 Q&As –> 1239 Q&As) [Lab Simulations Available]
P.S. Free 2020 CCIE/CCNP 350-401 ENCOR dumps are available on Google Drive shared by PassLeader: https://drive.google.com/open?id=1nv6C6Az-yuR5kOXg8FV3gytDer_usQBX






